Charities unprepared for cyber attack risk

Simply sign up to the Cyber Security myFT Digest -- delivered directly to your inbox.
In January 2017, Little Red Door, a small US healthcare charity, received an ominous email with “Cancer Sucks, But We Suck More!” as the subject line. Hackers had blocked access to the client files and financial data of the Indiana-based organisation and were demanding money for its release.
Little Red Door opted not to pay the bitcoin ransom (equivalent to about $43,000), as it did not keep sensitive information, such as bank account details or social security numbers. However, it had to spend months rebuilding its client data.
The size of the charity and its social mission — providing services to people in its area who have a cancer diagnosis — showed how undiscriminating cyber criminals can be in choosing their target.
Yet while the chances of being hacked are as high for a charity as for any other organisation, the non-profit sector is unprepared to meet cyber threats.
In a 2016 survey by US accounting firm CohnReznick, almost half of the non-profit organisations polled said they had not completed a cyber-risk assessment in the past year and 66 per cent had no plan to increase their spending on data security.
While it is not surprising that charities want to spend scarce resources on housing the homeless or feeding the hungry, some argue that those very services could be at risk if they fail to invest in cyber security tools and practices.
Part of the problem is that non-profit organisations do not put a price on not being able to operate, says Ken Montenegro, IT director at advocacy group Asian Americans Advancing Justice. “Non-profits don’t have a good analysis of down time,” says Mr Montenegro, who is part of a cohort of IT directors from advocacy organisations who collaborate on cyber security.
In addition, he says, IT budgets are often spent on areas such as communications, seen as key to fundraising, rather than cyber security. “That puts us in a precarious position because we’re not used to spending on something like a patch management tool that keeps our software up to date,” he says.
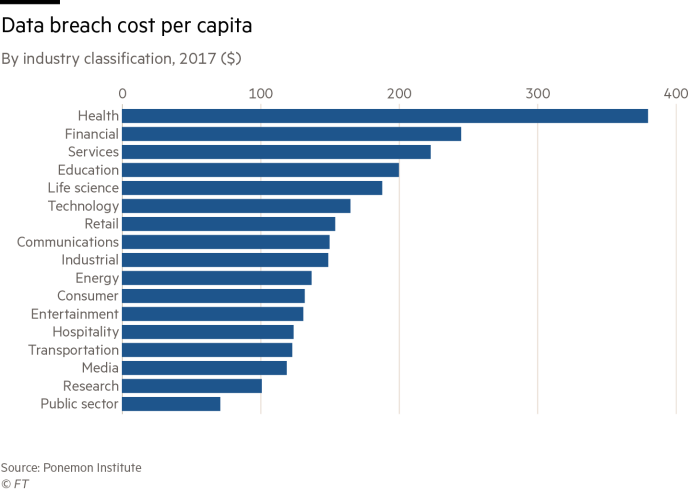
However, the costs of being unprepared can be high, something charities can ill afford.
When breached by ransomware, the potential human cost of being unable to deliver services means the pressure for non-profit organisations to pay off the hackers is intense.

Last year, for example, a Los Angeles non-profit hospital paid a bitcoin ransom equivalent to about $17,000 to regain access to the medical records of its patients after hackers attacked parts of its network.
Statistics on the number of charities being hacked are hard to obtain, since many organisations do not report these incidents. However, in the rising tide of cyber crime — which research company Cybersecurity Ventures predicts will cost the world $6tn a year by 2021 — non-profit organisations are certainly not excempt.
Nor is it only the data of the clients they serve that charities need to worry about. As online giving has swept through the non-profit sector, it has also created new risks.
Because they permit very small donations to be made online, for example, non-profits are frequently the target of credit card fraudsters who use donation forms to check if stolen credit card details will work.
“As long as there have been online donations, there’s been online donation fraud,” says Steve MacLaughlin, vice-president of data and analytics at Blackbaud, which provides non-profit organisations with software and services.
While charities have benefited from allowing very small donations to be made online, they now need to balance this with deterring the fraudsters. Mr MacLaughlin says that raising the minimum gift amount is one way of doing this.
He adds that charities could also deflect fraud attempts by making more use of the address verification systems (AVSs) provided by credit card processors. Again, charities need to strike a balance. While many of them lower verification levels to make it easier for donors to give online, particularly overseas donors, this reduces their protection.
“A simple answer is to turn up the AVS, so if you don’t have an address corresponding to the credit card it rejects it,” says Mr MacLaughlin. “That’s a setting that non-profits are often not aware of, or they turn it off.”
Another challenge is protecting donor data, particularly since charities use many online donation channels, says Amy Sample Ward, CEO of the Non-profit Technology Network, which offers training in technologies such as digital fundraising and online branding.
“With the rise of giving days, events and fundraising platforms that connect to social media sites, there are many different channels through which someone may give an organisation money,” she says. “Then that data is out there in so many ways.”
Given that employee errors are a leading cause of data breaches, Melanie Lockwood Herman, executive director of the Virginia-based Non-profit Risk Management Center, stresses the need for organisations to train all staff on the risks and consequences of data breaches.
She advises them to adopt policies that ensure information the organisation collects is accessible only to those who need it. This, she says, is important for non-profits, since they hold information on a broader range of constituents than companies.
“For-profits have employees and customers but they might not have donors or volunteers,” she says. “So there’s a couple of additional stakeholder groups [for non-profits] whose personally identifiable information is collected.”
One solution is to store data in the cloud with a trusted vendor. “Using servers owned by others is a huge reduction in cost and you can benefit from the expertise of a larger organisation,” says Ms Lockwood Herman, although she adds that non-profits should ask vendors about the security measures they have in place before signing the contract.
The outsourcing model also works well when it comes to managing online donations.
“You don’t need to build all these tools and then bring experts in to make sure they’re secure,” says Ms Sample Ward. “PayPal has figured that out.”
Above all, says Mr MacLaughlin, charities need to recognise the importance of protecting the data they have on supporters. “It is probably the most valuable asset on their balance sheet,” he says. “And because it’s so valuable, they have to have certain safeguards in place.”
Comments