UK retailers need to pay ‘serious attention’ to online weak points

Simply sign up to the Cyber Security myFT Digest -- delivered directly to your inbox.
Retailers know how devastating a cyber attack can be: only two years ago, on the other side of the Atlantic, the chief executive of Target resigned after hackers stole the personal information of 70m customers.
Last year, according to the British Retail Consortium, fraud and cyber crime against retailers rose 55 per cent. “The majority of retailers were victims of some form of cyber attack in 2014/15,” the BRC said.
With more and more shoppers moving online, having a safe website is vitally important.
Two-thirds of companies told the BRC that they felt their defences were in “good to excellent” shape. Retailers have invested millions in online defences and cyber experts.
But according to UpGuard, a Silicon Valley company that has developed some of the most advanced technology to assess whether websites are safe, many British retailers need to pay “serious attention”.
The Financial Times asked UpGuard to assess the risks of using UK websites and the cyber security group responded by saying that customers should be on guard when passing “sensitive information” to many of the sites.
UpGuard is used by thousands of companies, including major groups like Cisco, the US networking company, Allianz, the insurer, and e*trade, the online broker, to detect online risks. It has partnerships with both Microsoft and Amazon.
Retailers responded by criticising UpGuard’s methodology, with many of them stressing that its scans did not fully take account of the internal security in place.
One of the key areas of dispute was the assessment that UK retailers do a poor job in encrypting all parts of a website. Many companies argue this was an unfair yardstick, saying they instead focus their security efforts on protecting core parts of their online systems, such as customer databases and payments pages.
But others in the security and technology industries have said much more needs to be done.
Earlier this year, Google security expert Parisa Tabriz said websites that use any unencrypted pages were “unsafe”. Companies including Twitter and Dropbox have supported a campaign to put “strict encryption measures on all network traffic”.

Greg Pollock, the vice-president of product at UpGuard defended its tests, saying that encrypting payment areas “does not absolve” companies from protecting the rest of their sites.
He said unless encryption were rolled out across a website, it can leave users vulnerable to strategies such as “DNS spoofing” or “cache poisoning” — strategies where users can be redirected to fake pages that appear to be legitimate, but can gather users’ details or spread computer viruses.
“It is true that external scanning only represents part of the information relevant to a site’s risk of breach,” said Mr Pollock. “But that is all consumers have to work from to determine a company’s digital security. Given such a short list of checks, you would expect companies to look better rather than worse.”
UpGuard also said it assessed companies to check whether they employed “email authenticity to prevent fraudulent messages”. This could help avoid online criminals impersonating company employees in order to defraud customers.
George Quigley, a partner at KPMG who specialises in cyber security, said retailers faced a complex environment, where they faced everything from “basic smash-and-grab credit card scamming through to very sophisticated attacks”.
He added that because customers tended to reuse the same password on several websites, even companies that invested in robust security could find that they were only as safe as their weakest rival.
But Mr Quigley said many retailers were investing in hardening their systems, setting up network security centres to watch for attacks around the clock. They were also devising algorithms that could tell whether, for example, a sudden surge of traffic was the result of a popular price promotion or a break-in attempt.
————————————————
The methodology UpGuard says it makes a “cyber audit” that uses publicly available information to assess a business. It looks at various factors. This includes the past breach history of a company. It tests whether a company employs “email authenticity to prevent fraudulent messages” being sent, by checking online records that help to reveal how well a company protects its communications. It also tests a company’s “attack surface” — the various points where a hacker may attempt to break into a site. The company looks to see if the company has up-to-date security certificates and whether the company employs encryption throughout its website.
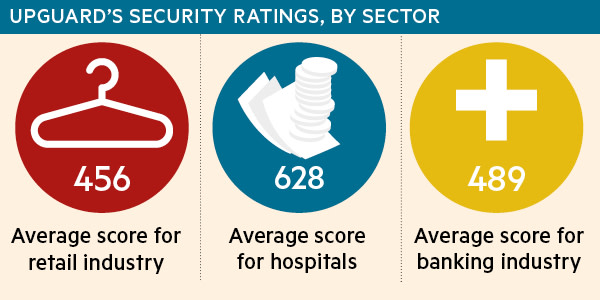
Through doing this “external scan” of a site, it determines a score — like a credit rating — on scale between 0 and 950.
————————————————
The UpGuard analysis did show some companies satisfying many of its tests. The best score was obtained by Aldi UK, which scored 846.
Other sites to score above 700 — a result that UpGuard said showed that a company took “website security seriously” and “has implemented most or all of the top controls” — were Amazon.co.uk and VM Morrison.
In separate research conducted for the FT, BitSight, a US company that measures how vulnerable companies are to cyber attacks, analysed whether UK top retailers had online security certificates, such as those required to ensure secure transactions, have been kept up-to-date.
Without these certificates, consumers are vulnerable to hacking strategies such as a “man in the middle attacks”, where a third party is able to access information such as credit card details during an exchange of information.
Of 19 British retailers surveyed, BitSight found that 68 per cent were considered “good”, meaning that most had security certificates in place. The UK fared better than the average of all global retailers of 43.7 per cent. However, only 26.3 per cent of the UK retailers had no certificate errors at all.
“Compared to all other industries, retail in the UK is doing better than most,” said Jay Jacobs, senior data scientist at BitSight. “But that doesn’t mean it is good. The other way to look at this is that 32 per cent had an error or flaw.
Comments