Big companies bring in the cyber bounty hunters

Simply sign up to the US & Canadian companies myFT Digest -- delivered directly to your inbox.
If you want to test the security of your IT systems, why rely on one expert when you could enlist thousands? Capturing the power of the crowd is the logic of bug bounty programmes, where organisations offer financial rewards to “friendly” hackers who find vulnerabilities in their networks.
The idea dates back to the early days of the internet, but has mushroomed in the past few years. The tricky part, experts say, can be finding out how much to pay a bounty hunter and knowing if they can be trusted.
At Bugcrowd, which manages bug bounty programmes on behalf of clients, payouts tripled to $4m in the year to March 2017, and the average reward increased to $451, compared with $295 the year before.
Casey Ellis, founder and chief executive of Bugcrowd, says the growth is being fuelled by the scarcity of security professionals and wider awareness of the bad things that can happen when flaws are left exposed. “Fear definitely plays a part, but it is probably more to do with responsibility and understanding [the threat],” he says.
Even so, many companies have yet to be convinced. Some 94 per cent of the Forbes Global 2000 companies do not have bug bounty programmes, according to HackerOne, another bug bounty management company.
The challenge, says Bugcrowd’s Mr Ellis, is persuading companies to work with hackers, “a community that security people have been taught not to trust”.
Technology companies pioneered bug bounty and offer some of the biggest rewards — up to $200,000from Apple and $100,000 from Microsoft and Google Chrome. This can mean rich takings for successful hackers. Six per cent of bug bounty hunters make over six figures a year, says HackerOne, with some hackers earning up to $900,000 annually. Average earnings, however, are less than $20,000 a year.
The idea of offering bug bounties is spreading to other sectors, including automotive, airline, financial services, retail, government, media and entertainment. Some 41 per cent of bug bounty programmes were from industries other than technology in 2016, says HackerOne.
Companies offering them include General Motors, Fiat Chrysler, Tesla, Lufthansa, Western Union, Starbucks, and the US Department of Defense.
Carmakers are paying the most among companies outside the technology sector, says Bugcrowd, with an average payout of $1,514, as they face up to the security risks posed by increasingly connected vehicles.
Organisations whose leaders are dubious about the idea often begin with “private” programmes in which only selected hackers are invited to participate.
This offers more control but fewer brains to tackle the problem. Once companies have tried this approach, they may move on to public programmes that are open to anyone and so provide the maximum chance of finding security loopholes.
Daniel Miessler director of advisory services at IOActive, a security consultancy, points out that in addition to sheer numbers of people, bounty programmes have the benefit of payment by results. “You don’t want to spend lots of money if people don’t find something,” he says.
But setting a price is difficult. There is a risk that the community will offer the bug to someone malicious if the bounty isn’t high enough, Mr Miessler says.
“It’s just like any marketplace. We have seen big names wildly change the bounty amount, depending on conversations they have when vulnerabilities are discovered.” The goal is to pay fairly close to what a researcher can get on the black market, he says.
Peter Sommer, an expert witness and professor of digital forensics at Birmingham City University, thinks that six-figure sums are often unnecessary.
“Anyway it would be difficult to match what they’d get on the black market,” he says. “I’ve [been a witness at] a couple of hacker cases where they’ve made an awful lot of money from denial of service attacks, certainly a lot more than you would pay a computer consultant.”
Many hackers hunt for bugs to supplement their income or fund their student expenses, others are based in developing countries where even modest payments go a long way, he says.
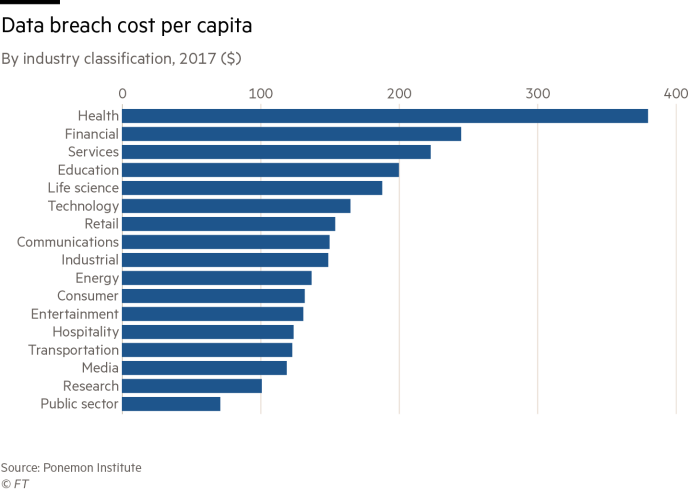
Eran Feigenbaum, chief information security officer at Jet.com, an e-commerce company, says deciding how much reward to offer should be based on the cost of a breach to your organisation.
In addition to being paid well, hackers need to be handled with respect, he says. “Treat them as security researchers until they prove otherwise.”
When they find security flaws, you should respond quickly. “Bounty hunters often get frustrated by being ignored, or by not receiving thoughtful acknowledgment,” says Mr Feigenbaum.
Mr Ellis says the 65,000 hackers on Bugcrowd’s books are more akin to locksmiths than burglars. “Locksmiths would make very competent criminals but they would rather use their ability to do good, be of help and stay on the right side of the law.”
Some malicious hackers are persistent, says Mr Sommer, but many people with those skills would rather make money “without having to resort to extortion and risk getting a criminal record or being extradited”.
However, he advises caution. “You need to employ them via a company that is going to offer you some guarantees and has insurance and enough capital that you can sue them if things go badly wrong.”
Comments